What are malicious Cryptominers? – How to prevent their menace

In the past, the majority of malicious Cryptomining codes tried to download and run an executable on the targeted device(s). However, a different form of Cryptomining malware has recently become very popular, which is, the browser crawling using simple JavaScript.
This method, also known as Cryptojacking, makes it possible to perform the same malicious activity directly in a victim’s browser, without installing any software.
Today, most cryptographic scripts and executables exploit Monero. This crypto-currency has many advantages over the better-known Bitcoin: it offers anonymous transactions and can be used with common processors and GPUs rather than expensive specialized hardware.
Both websites and computers have been a victim of this malware. Cryptomining and Cryptojacking cyber-attacks have been detected on all popular desktop platforms, as well as Android devices. Most are classified as Potentially Unwanted Applications (PUAs); however, some of the detected attacks fall into the more dangerous category of Trojan Horses.
As far as websites are concerned, Astra Security has written a detailed guide on website crypto-malware. The guide can help users in removing Cryptojacking CoinHive Malware from their WordPress, Magento, Drupal & Prestashop websites.
How Crypto malware infects computers & phones?
Crypto-mining viruses are known to infect computers, including undermining Monero. But here, botnet-like malware specifically targets Android devices.
This new malware seeks to build a network of computer bots (botnet), with the main goal of undermining Cryptomonnaies without the knowledge of its victims.
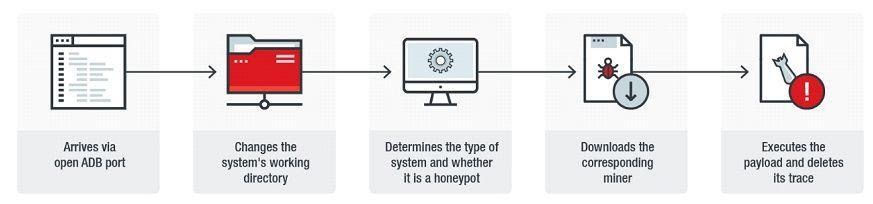
Whenever you visit an infected page, the virus attempts to exploit open ports on your device, normally intended for the Android Debug Bridge (ADB) feature, which allows you to fix bugs in applications installed on Android phones and tablets.
The malware then changes the directory for the attack to a less secure one and downloads crypto-mining software suitable for the device and then starts the device to run. Once its malicious task is completed, it takes the time to erase its tracks to reduce the risk of detection and then deletes itself.
In addition, the malware attempts to spread to other Android devices based on all the exchanges that the infected device has made. The virus has already been detected in 21 different countries, with South Korea currently being the most affected region.
How Crypto malware infects websites?
For websites, the effects are even more disastrous. The crypto-malware uses your server resources to its advantage. This causes a decrease in load time and even website downtime for you. Cases have been reported where people using solutions like AWS got billions of 10x their usual bills for the resources crypto-malware was eating up.
How to recognize a Crypto Mining attack?
Cryptomining and Cryptojacking are associated with extremely high processor activity, which has significant side effects. Victims often report visibly reduced device performance, overheating, and increased fan activity (and therefore noticeable noise).
On Android devices, the computational load can even lead to a “swelling” of the battery and thus to physical damage or destruction of the device.
Similar complications can be caused by a variety of hardware or software problems; however, in the case of Cryptojacking, they become apparent after the victim has accessed a specific Web site – probably one that incorporates the JavaScript code of Cryptomining.
How can you protect yourself from malicious crypto Miners?
Use a reliable, multi-layered security solution to block unwanted Cryptomining and Cryptojacking activities. If you notice that access to a specific website significantly increases your CPU usage, close the browser.
In some cases, a reboot may be necessary to close hidden browser windows, which continue with background browsing. After rebooting, do not allow your browser to automatically load the previous session, as this could reopen the Cryptojacking tab.
Discuss this news on our Telegram Community. Subscribe to us on Google news and do follow us on Twitter @Blockmanity
Did you like the news you just read? Please leave a feedback to help us serve you better
Disclaimer: Blockmanity is a news portal and does not provide any financial advice. Blockmanity's role is to inform the cryptocurrency and blockchain community about what's going on in this space. Please do your own due diligence before making any investment. Blockmanity won't be responsible for any loss of funds.














